Cloaking is a search engine optimization (SEO) technique in which the information or content presented to search engine crawlers (i.e. bots or spiders) is different from the information presented to users. It is done to achieve better indexing.
Cloaking is an illegal practice as it is a way to cheat. Cloaking in SEO is considered as a Black Hat SEO. In this technique, a web server is programmed in such a way that it returns to other content for search engine robots than it does for a regular user, by creating cloak content and altering search rankings. Search engines permanently ban such websites from their index.
How Is Cloaking In SEO Done?
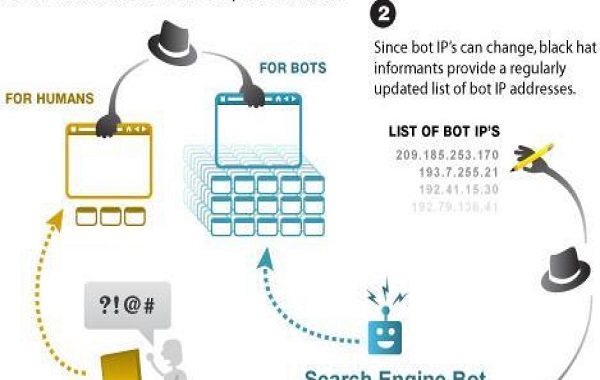
So, you must be aware that every internet device such as tablets, computers, mobile phones, etc. are identified by an IP address. If cloaking is used, the content would be delivered based on User-Agent HTTP header or IP address of the user requesting the page. In cloaking, a file called .htaccess is modified. There is a module called mod_rewrite in apache server, which lets you apply the cloaking in SEO technique to the web pages.
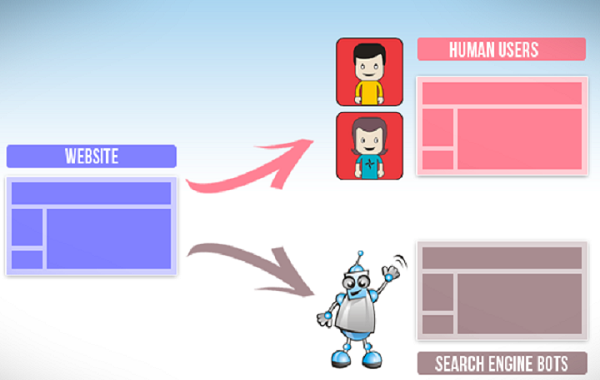
The webmasters collect search engine’s User-Agents or IP address. If mod_rewrite module finds that a User-Agent or IP address belongs to a search engine, a different form of the web page (cloak URL) is delivered by a server-side script. In case the IP address does not belong to any crawler, it implies that it is a regular visitor and displays a normal web page.
In simpler terms:
- Websites that engage in cloaking prepare two types of content. One out of the two is targeted for human visitors and the other one is targeted for bots. Bots are detected by their IP addresses.
- Black Hat informants present a regularly revised list of bot IP addresses.
- Bots are provided with ample fabricated content loaded with targeted keywords, which boost rankings.
- As a result, a human visitor does not find useful information even though the ranking of the website is high.
Cloaking in SEO: Some Common Practices

Now that you know what cloaking in SEO means, the next thing to understand is the type of content webmasters show differently to search engine crawlers and users. You must be aware that search engine indexes a web page, and based on META tags, titles, etc., it ranks it in SERPs (search engine results page.) Considering this, webmasters optimize these basic things:
- Hidden text
Webmasters include additional information such as keywords stuffing, overwriting content in such a way that it is hidden to the users. For doing so, webmasters add this information in the exact color as the background color to make it invisible to human eyes. This is one of the most popular cloaking in SEO technique.
- Cloaking in e-mail
The address and name of the sender of an e-mail are masked through cloaking in e-mail distribution. So, the recipient cannot know who is the sender of the e-mail.
- Flash-based websites
As per SEO guidelines, using flash is not recommended. However, several websites require multiple flashes and are built in flash only. So, rather than rewriting everything in HTML and rebuilding websites, they build content-rich web pages and give them to search engine crawlers and provide visitors with flash pages.
- Image Gallery Websites
Such websites have a significantly higher number of images than real content on their pages. Crawlers do not scan images, and so, webmasters believe that cloaking would help them achieve top placement for relevant keywords.
- HTML rich websites
A good SEO recommends that your web page should have more content (text) in comparison with your HTML tags. So, one must maintain a high TEXT to HTML ratio. So, if anyone writes insufficient posts or articles, their TEXT to HTML ratio would be low. To avoid rebuilding the websites, people choose cloaking in SEO to meet the SEO guidelines.
Which Of The Cloaking In SEO Practices Are Allowed?
There are several cloaking in SEO techniques that are allowed, which display different information about the content to different users.
First Click Free
Users can read the web page without having to register with or pay the hosting website just by clicking it on Google. Using this method, you let Googlebot pass as a registered member as well as allow users coming from Goggle’s search list through.
Geo-IP Location
In this, content is displayed to the users on the basis of their location. For example, in Google’s case, you will find that if you make a search from your country for SEO, it will show a different result from the one it would present had you made the search from another location or country. This is not a Black Hat SEO technique, as it is done to provide an enhanced user experience. So, practicing this is perfectly fine for any webmaster.
Replacement of Java scripts
In this, JavaScript is used to display content to non-JavaScript visitors, which matches the content within Flash or other multimedia element.
URL rewriting
This includes discarding unnecessary parameters and other URL. This is not a Black Hat SEO practice as it does not change the underlying content, and it is acceptable to present another URL for specific content to make it more search engine friendly.
Key Takeaway
Most search engines are completely against cloaking. Search engine algorithms are ever-changing and are more intelligent than we are. They are bound to find malicious techniques used by websites to increase ranking. Therefore, it is advisable to stay away from cloaking techniques.